When selecting which browser to use to enhance productivity, users basically refer to HTML 5 compliance, one of the benchmarks to gauge a browser’s speed. The higher the mark, the faster the browser. Against this backdrop, Google Chrome comes bustling with 463 points out of 500, followed by Opera with 404 points, Firefox with 393, Internet Explorer […]
Tech Guide
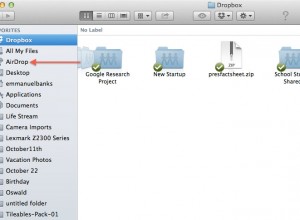
The Ultimate Guide to Sharing Everything on Mac
Your Mac is a powerhouse for networking and sharing. From the usual capabilities that we are used to, like the ability to share printers to unique features like AirDrop, Mac allows for multiple ways to share between computers. However, not all Mac users know where these opportunities lie.
Google Reader Shutting Down on July 1; Here are 5 Alternatives
In its latest round of Spring Cleanup Google has waved a red flag on quite a few of its services including Google Reader – the RSS reader service which was launched back in 2005.
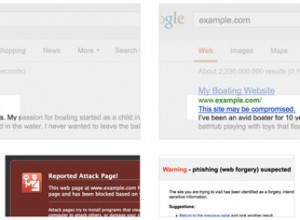
Google launches Help for Hacked Sites Series with articles and videos
With the passage of time, DDoS attacks and hacking attempts have increased a lot and many people are falling victim to this act and losing their site and valuable data to hackers.
What Are TED Conferences: Your Ultimate Guide
Have you ever had an issue or subject you are extremely passionate about, or a thought you wanted to share but didn’t have a venue to share it. The TED conference is that venue for influential individuals, movers, and shakers in a certain subject.
How to Survive Working in an Office
In Silicon Valley, the technology hub of the United States, being able to work from home is a luxury not all companies offer.