Researchers from the Georgia Institute of Technology have discovered a weak spot in the connection between an iOS device and computer that leaves data in transit vulnerable to third-party manipulation and breach.
As the scope and impact of mobile malware continue to grow, the Android operating system is most commonly hit by a spate of attacks that come in many forms and techniques, often relying on vulnerabilities that are left unattended on mobile devices. That is so because of the platform’s unmatched popularity worldwide.
But with iOS devices becoming increasingly a target among attackers, there should be a polarization of security measures to fend off threats on the Apple devices. Gone are the days when the iOS ecosystem is a malware-free environment.
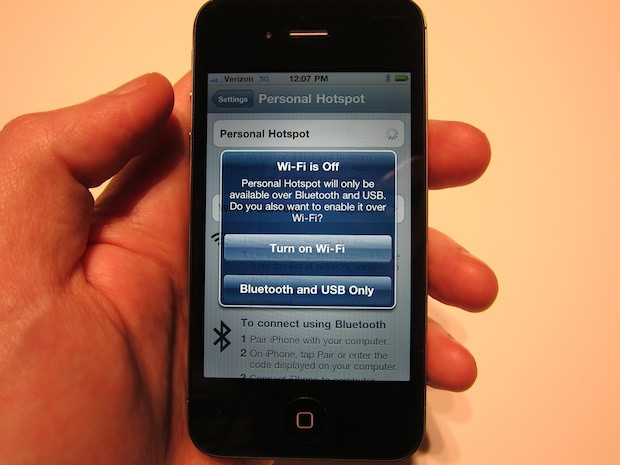
That is nowhere near more evident than in the latest discovery of Georgia Institute of Technology researchers. The findings indicated that iOS devices – smartphones and tablets – are open to security breaches when they are connected to external devices such as computers to synchronize files and functions. The connection may be in the form of a wireless network or a USB cable.
As a result of this insecure connection, the data carried through these links become an easy target for hackers and attackers. As is often the case, the weakest link here is you as the user. There is hardly any indication or red flag when the connection between your iPhone and a computer is being compromised because the operation happens generally in the background.
Read also: Data-dumping feature on iOS revealed; close relationship with NSA spying tools possible
Naturally, the iOS devices have no functionality to alert users of a possible hack when it is connected to an external device. During the process, an iOS device cannot tell you that there is an ongoing data breach or if a malware is making its way to your device. When that happens, hackers could maneuver your device into downloading more botnets and viruses without you knowing it.
There could be a myriad of ways through which data moving from your iOS device to a computer could succumb to hacking, but the most common are these: Attackers could use your personal Apple ID or manipulate a developer certificate in order to purport that an app is legit and so convince the iOS device to download that app.
Fortunately, there are also ways to prevent this from taking place. First, you must avoid connecting your iOS device to computers that is of public use. Second, install robust security software on your device. Finally, as much as possible avoid jailbreaking your iPhone or iPad, as we have always said, because it could potentially open back doors to hackers.



