The FBI made headlines last month when it said it had taken down the CryptoLocker ransomware in collaboration with European law enforcers, along with the seizure of command and control servers used by hackers to operate the GameOver Zeus botnet, through which the ransomware was spread.
While there is no doubt to the fact that, indeed, those servers busted by the authorities are no longer functional for the attackers, some important facts have been missed by the FBI, such as that the myriad of botnets other than the ones they were able to take down are still at large, going on with their usual malicious operations.
Read also: A wave of old ransomware targeted Android devices this week
As a matter of fact, a new ransomware has been spotted to be on sale in the black market. The malware, called Critroni, is being sold for $3,000 and reports had it that the ransomware is being unloaded by the Angler exploit kit. According to security researchers, Critroni is the first ransomware that takes its root in CryptoLocker and uses the Tor command and control network.
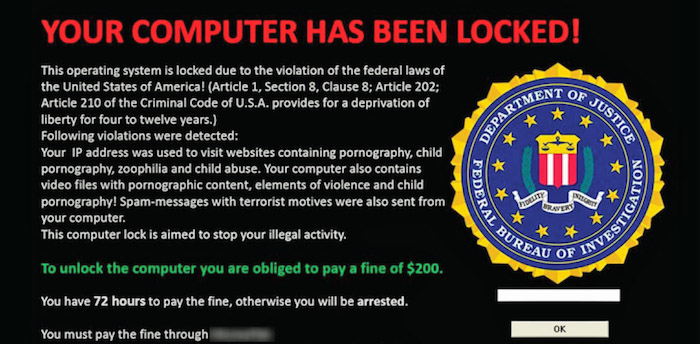
Security researcher Tyler Moffitt claimed that the FBI failed to completely neutralize CryptoLocker from communicating with the command and control infrastructure used to run the ransomware. In fact, he said, the host of servers that the FBI seized only represented a small sample of the infrastructure which has been targeting hundreds of thousands of computers, locking the system and asking a ransom from the victim users in exchange for the key to recover their computer.
Aside from Evgeniy Bogachev, the mastermind behind the GameOver Zeus botnet operation, Moffitt argued that Bogachev’s cohorts were also able to distribute adapted versions of the ransomware, so only those servers controlled by Bogachev were the ones that no longer work. The rest are still alive and many other hackers have begun to use it following the FBI takedown that made buzzes recently.
Those other malware authors now have disseminated the various crypto malware like CryptoWall, New CryptoLocker, DirCrypt, and CryptoDefense. It could be that other malware writers are also distributing their ransomware through botnets that they themselves gathered or rented from other creators of botnets. The second scenario best describes the present situation, since Bogachev’s servers have been busted, other malware authors only have the option to rent from other botnets that still operate.
There are noticeable changes such as the parting away with a third-party money transfer firm or money mule. Now cyber criminals are able to receive the profit from their malicious activity through a direct channel.



