When you are in the business of handling the critical enterprise applications of large public companies, any instance of security vulnerabilities should make you respond to it quickly. Quite the contrary for SAP.
Onapsis’ security researchers uncovered more than a dozen of security flaws in the SAP HANA in-memory database management platform services that process applications for businesses. The good news, though, is that SAP has already patched these vulnerabilities and issued guidance for configuration issues found in the platform.
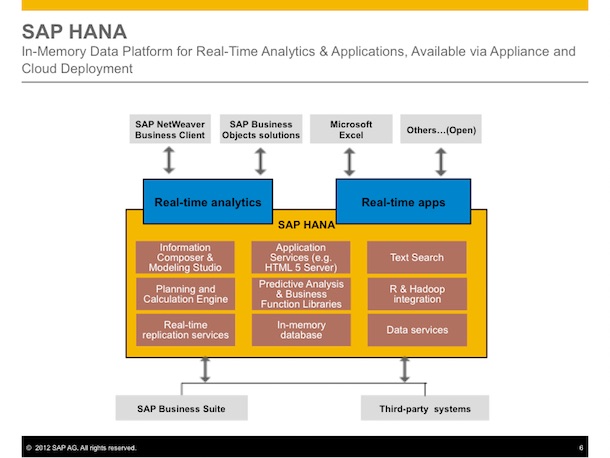
However, Onapsis lamented that SAP failed to pay mind to these vulnerabilities that grew in number over the past year as made manifest by various reports about affected business applications. SAP HANA powers the tools that the Fortune 2000 companies use to manage scientific data and critical assets.
In other words, the critical issues in SAP HANA lack the attention needed to address them. Onapsis said there had been a lot of security measures missing in place and that even the people and teams who should pay attention to these issues did not have sufficient concern for the vulnerabilities long discovered to affect this platform.
Chances are that if these tools are left unattended because of the wide distribution of duties, cyber criminals and state-sponsored hackers will find a way to hack into these systems for a variety of purposes.
More specifically, some of the critical security flaws involve the TrexNet administrative interface found in SAP HANA installation that is responsible for granting execution approval for various business operations. Because of the default configuration in the interfaces, some business functions are potentially exposed to remotely executed attacks.
The problem is addressed through a new configuration. If these functions are exposed, attackers will be able to gain a full view of a company’s enterprise data and manipulate it for their own gains.
Onapsis advises users who would be installing SAP HANA for the first time to configure the parameters in order to close the interfaces, which are open by default. Also, the communication for several servers must be conducted on a private network.
Fortunately for SAP HANA clients, several memory corruption and SQL-based flaws have been fixed already, consequently preventing a remote code execution and denial-of-service attacks from taking place. Also, there has been no known exploits in the wild as of this time, so everyone using the platform is relatively safe at the very least.
While the critical vulnerabilities have been patched, the security researchers vow to carry on with their study of the applications to find, if ever, more flaws in order to address them.



