From 2014 to present, point-of-sale system hacks have topped the recorded data compromise cases in North America, owing to the growing application of chip-based payment methods in the region.
That’s according to the results of a study conducted by Trustwave. In Europe, Middle East, Africa and the Asia and Pacific regions, the frequency of hacked PoS terminals are relatively low due to the lack of mandate for electronic chips to prevent fraud.
In either case, the risks are high. You have PoS applications in North America, you also face an increasing wave of cyber attacks while minimizing fraudulent financial activities. On the other hand, you have fewer PoS services in other regions, you run into higher rates of fraud while keeping safe from targeted attacks.
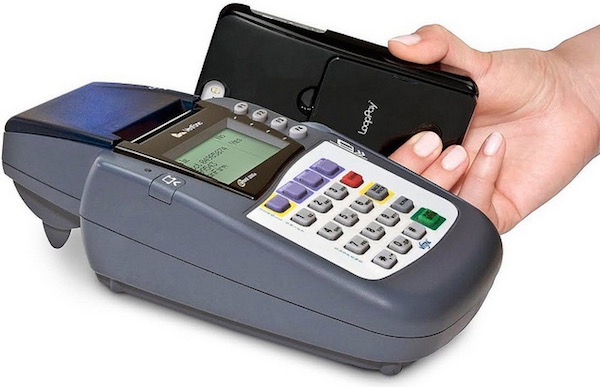
This chip-based payment system works to validate cards that use Europay, Mastercard or Visa, thus making it difficult for any attacker to perpetrate their malicious plans. Some cyber criminals would clone the cards to steal data and eventually the money that goes with it.
Fraudulent tactics have also turned to online transactions from the previous focus on financial transactions where cards are physically present. That is why a lot of cases of cyber hacking nowadays involve e-commerce websites, from which card data are of significant value to criminals.
Specifically, card track data and PoS terminals are the primary goals of cyber attacks in the United States. Part of the problem is that the security systems used by Europay, Mastercard and Visa only work to prevent fraud and not to fend off security threats. It pays to always be aware that chip-based cards do not necessarily protect cardholder data.
Beginning in 2013 through 2014, Trustwave observed a spate of PoS system breaches and e-commerce attacks, and the figures are rising. Other businesses that appeared to have been targeted by cyber attacks included retail, hospitality, and food and beverage. In all these variants of attacks, PoS terminals were the favorite target of the bad actors in an attempt to extract valuable information from the treasure chest.
Majority of those breaches saw e-commerce transaction data such as personal identifiable information and cardholder data compromised. The cyber crimes were perpetrated via attack methods like insecure remote access software and password brute-guessing, which sheds light on the lack of some users in terms of formulating strong passwords.
Weak passwords accounted for majority of these security failures due to the remote administration configuration of the PoS terminals over the Internet or a private network.



